Do business safely
A rigorous and transparent cybersecurity labelling methodology
The rating guide details the procedures and more than 1300 practices analysed to determine the rating of the safety levels provided by the providers in each department.
The methodology is based on a supervised self-declaration, which assumes that it is the ICT service provider itself that chooses the level at which it wishes to qualify its service. The provider have to fill out a report in which it defines how it complies with the practices required for that level, and that it is audited by LEET Security to verify that the proposed level is adequate.
The rating methodology is the first comply with the standard "UNE 71381:2016 Information technology. Cloud Computing. Labelling systems" which establishes the requirements that labelling systems such as LEET Security must meet.
Procedure
The procedure, after acceptance of the conditions by the supplier, is carried out in the following phases:
Rating
The ratings granted consist of 3 letters, which define the rating obtained by the provider for the given service, in the three fundamental dimensions of Confidentiality, Integrity and Availability of the information. All ratings are registered and made public on the LEET Security website and its broadcast channels.
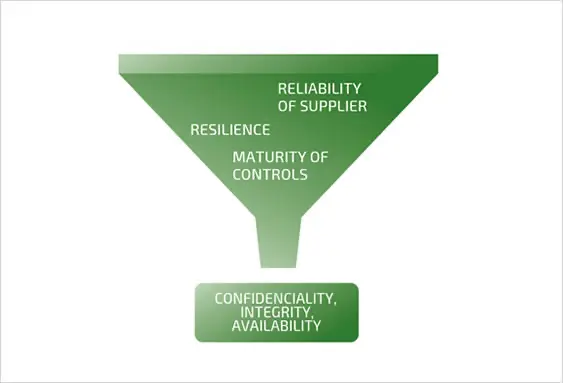
Both the specific measures implemented by the provider in the rated service and the provider’s general characteristics are taken into account when awarding these rating levels, to ensure that the provider is reliable. The measures implemented to ensure the resilience of the service provided are also assessed (as no one is immune to incidents, the most important factor is to evaluate the service’s ability to recover).
Follow up
Monitoring to ensure that the required conditions are maintained during the validity period is carried out based on three additional control mechanisms:
Conducting random periodic audits.
Digital surveillance, including reporting channel by users of qualified services.
Obligation of the supplier to notify LEET Security of any circumstances or modifications that may affect the rating.
In either case, LEET Security would proceed with a reassessment in order to determine whether maintenance or modification of the rating levels granted to the service.
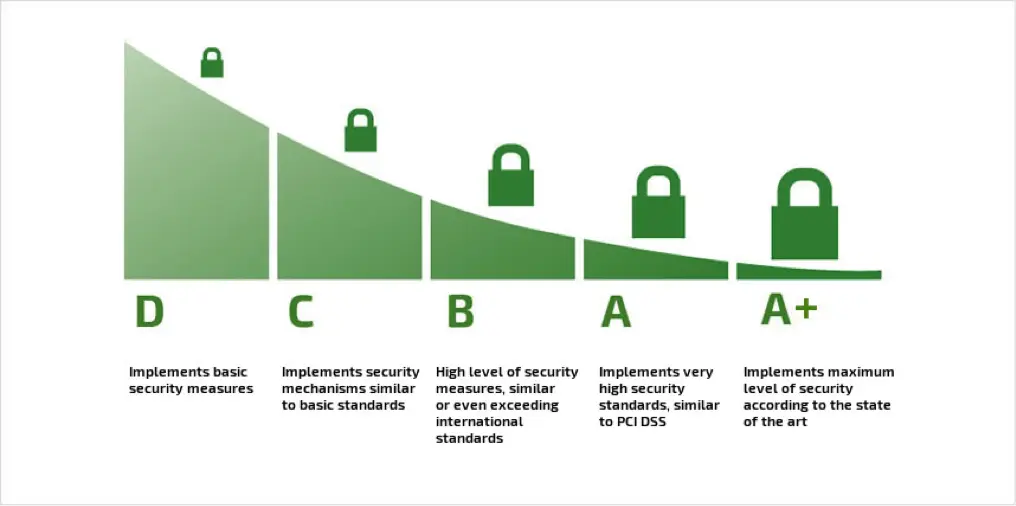
Rating levels
All the practices included in the rating guide are classified into 5 tiers, from A+ to D; requiring compliance with basic safety measures from Level ‘D’ and corresponding Level ‘A+’ to the best possible set of measures at any given time. In this way, the ‘A+’ level is reserved for those services intended for the processing of extremely confidential information (such as industrial or national secrets) or with very demanding availability requirements (such as critical infrastructures).
To reach a certain level, it is necessary to comply with all the practices required for it, taking into account that “security is as strong as the weakest link”. This implies that if a service meets all but one of the practices required to achieve Level B where it meets the Practices for Level C, the final rating will be a C.
Having the LEET Security seal ensures that the qualified service has a management system and security measures.
This rating is not global, but measures the three relevant fundamental dimensions of information security are evaluated: Confidentiality, Integrity and Availability. In this way, the rating granted by LEET Security consists of three letters: The first indicates the reliability of the service in terms of Confidentiality, the second assesses Integrity and the third measures Availability, always specifically for the qualified service.
Our rating system has also set a special benchmark for different standards. In this version of the methodology there are six special supplemental compliance qualifiers:
+DORA (DORA Passport) indicating the degree of compliance with the requirements established by the European DORA (Digital Operational Resilience Act) regulation. It includes a Cyber Resilience Index, indicating the degree of implementation of cyber resiliency measures, between 0 and 1000, in two levels, DORA Prime (between 500 and 749) and DORA Elite (between 750 and 1.000).
+NIS2 (NIS2 Passport) which provides a complete assessment of the requirements set out in NIS2
+PRIV, is granted after verifying that all the practices linked to the data protection regulations are complied with, and in particular with the General Data Protection Regulation and the LOPDGDD, according to the rating obtained.
+C4V, indicates compliance with the Cybersecurity capacity building model for the supply chain, in accordance with ENSI
+ENS/c, indicating compliance with RD 311/2022, which regulates the National Security Scheme.
+PCI, implies that the service complies with PCI DSS v3.1.
We can also come across the non-specific rating: PASSED. This means that the service in question at least exceeds all of the measures corresponding to level D in all three dimensions, although the supplier does not want to show the levels explicitly. In this case, the executive report of the corresponding levels can be consulted in the Qualified Services section, associated with the corresponding registration number, or by clicking on the seal shown on the website of the service provider.
Recognition
Developed since 2010 and continuously evolving, LEET Security’s rating system is recognized by the European Agency for Network and Information Security (ENISA) and is registered as a trusted instrument by Instituto Nacional de Ciberseguridad (INCIBE).



